I’m pretty new to selfhosting and homelabs, and I would appreciate a simple-worded explanation here. Details are always welcome!
So, I have a home network with a dynamic external IP address. I already have my Synology NAS exposed to the Internet with DDNS - this was done using the interface, so didn’t require much technical knowledge.
Now, I would like to add another server (currently testing with Raspberry Pi) in the same LAN that would also be externally reachable, either through a subdomain (preferable), or through specific ports. How do I go about it?
P.S. Apparently, what I’ve tried on the router does work, it’s just that my NAS was sitting in the DMZ. Now it works!
Welcome to the wonderful world of reverse proxies!
If you mean HTTP server, what you need is a reverse proxy and name-based virtual hosts. I usually use nginx for such tasks, but you may choose another web server that has these features.
Best solution you most likely want to go for. Or use multiple ports.
Thanks!
I recommend caddy as a webserver, it’s very powerful, but the config is super simple compared to old school stuff like nginx or apache.
Heard quite a few positive reviews on that one, thanks!
Router gets the public IP. Login to it, find port forwarding option. You’ll pick a public port. IE 443 and forward it to a local IP:port combo, IE 192.168.0.101:443.
Then you can pick another public port and forward it to a different private IP:port combo.
If you want a subdomain, you forward one port to one host and have it do the work. IE configure Nginx to do whatever you want.
EDIT: or you use IPv6. Everything is a public IP.
Thanks!
Looks like you got it! Congrats.
Yup
Or he just uses a reverse proxy like nginx. So all can be hosted behind the same port (443)
Not yet, but want to figure it out properly.
I would use Caddy or something else that is less complex to setup
Yeah Caddy is also a great option.
Something we didn’t had a decade ago. Then the most likely approach was either apache or nginx.
VPN is definitely the way to go for home networks. Your router even has one built in. OpenVPN and Wireguard are good.
If you really want to expose stuff like this the proper way is to isolate your home network from your internet exposed network using a VLAN. Then use a reverse proxy, like caddy and place everything behind it.
Another benefit of a reverse proxy is you don’t need to setup https certs on everything just the proxy.
You do need a business or prosumer router for this though. Something like Firewalla or setting up a OpenWRT or OPNsense.
Synology also has there quick connect service as well. While not great if you keep UPNP off and ensure your firewall and login rate limiting is turned on it may be better then just directly exposing stuff. But its had its fair share of problems so yeah.
Consider not self hosting everything. For example if all your family cares about is private photo storage, consider using a open source E2EE encrypted service for photos on the cloud like Ente Photos. Then you can use VPN for the rest. https://www.privacyguides.org/ has some recommendations for privacy friendly stuff.
Also consider the fallout that would happen if you are hacked. If all your photos and other things get leaked because your setup was not secure was it really any better than using big tech?
If nothing else please tell me you are using properly setup https certs from Let’s Encrypt or another good CA. Using a firewall and have login rate limiting setup on everything that is exposed. You can also test your SSL setup using something like https://www.ssllabs.com/ssltest/
No truly private photos ever enter the NAS, so on that front it should be fine.
VPN is not an option for several reasons, unfortunately.
But I do have a Let’s Encrypt certificate, firewall and I ban IP after 5 unsuccessful login attempts. I also have SSH disabled completely.
SSL Test gave me a rating of A
Who is externally reaching these servers?
Joe public? Or just you and people you trust?If it’s Joe public, I wouldn’t have the entry point on my home network (I might VPS tunnel, or just VPS host it).
If it’s just me and people I trust, I would use VPN for access, as opposed to exposing all these services publicly
Just me and the people I trust, but there are certain inconveniences around using VPN for access.
First, I live in the jurisdiction that is heavily restrictive, so VPN is commonly in use to bypass censorship
Second, I sometimes access my data from computers I trust but can’t install VPN clients on
Third, I share my NAS resources with my family, and getting my mom to use a VPN every time she syncs her photos is near impossible
So, fully recognizing the risks, I feel like I have to expose a lot of my services.
What are you running?
If it is http based use a reverse proxy like Caddy
Update: tried Caddy, love it, dead simple, super fast, and absolutely works!
Did you also forward UDP port 443?
If not I would as well since it is used for QUIC which is supported and automatically turned on for Caddy.
Yep
For now just some experiments alongside NAS
Planning to host Bitwarden, Wallabag and other niceties on the server, and then when I get something more powerful, spin up Minecraft server and stuff
Whispers “try proxmox”
I will eventually!
But for all I understand, it is to put many services on one machine, and I already have a NAS that is not going anywhere
I’ve gone the other way. I used to run a Proxmox cluster, then someone gave me a Synology NAS. Now it’s rare that I spin up Proxmox and instead use a mix of VMs, containers and Synology/Synocommunity apps.
Interesting!
But I don’t want to mix it too much. I do have a Docker on it with just some essentials, but overall I’d like to keep NAS a storage unit and give the rest to a different server.
I treat NAS as an essential service and the other server as a place to play around without pressure to screw anything
I really feel like people who are beginners shouldnt play with exposing their services. When you set up Caddy or some other reverse proxy and actually monitor it with something like fail2ban you can see that the crawlers etc are pretty fast to find your services. If any user has a very poor password (or is reusing a leaked one) then someone has pretty open access to their stuff and you wont even notice unless you’re logging stuff.
Of course you can set up 2FA etc but that’s pretty involved compared to a simple wg tunnel that lives on your router.
My mantra is “plan to be hacked”. Whether this is a good backup strategy, a read-only VM, good monitoring or serious firewall rules.
For now I’m only toying around, experimenting a little - and then closing ports and turning my Pi off. I do have my NAS constantly exposed, but it is solidly hardened (firewall, no SSH, IP bans for unauthorized actions, etc. etc.), fully updated, hosts no sensitive data, and all that is important is backed up on an offline drive.
If you go with IPv6, all your devices/servers have their own IP. These IPs are valid in your LAN as well a externally.
But it’s still important to use a reverse proxy (e.g. for TLS).
Oh, nice! So I don’t have just one, but many external IPs, one for every local device?
Yes, even IPv4 was intended to give each device in the world their own IP, but the address space is too limited. IPv6 fixes that.
Actually, each device usually has multiple IPv6s, and only some/one are globally routable, i.e. it works outside of your home network. Finding out which one is global is a bit annoying sometimes, but it can be done.Usually routers still block incoming traffic for security reasons, so you still have to open ports in your router.
Nice to know!
You already have a lot of good answers … but I got one more to add.
I have a very similar setup on my homelab and I’m using a Cloudflare tunnel.
It’s a free service and it’s really good because it allows you to expose web services and specific ports for remote access over dynamic IPs without having to expose your own router.
https://developers.cloudflare.com/cloudflare-one/connections/connect-networks/
Thanks! I got that advice as well, but I would like to keep it self-hosted - I consider using Pangolin on a VPS for that purpose going forward: https://github.com/fosrl/pangolin
Also, beware of the new attack on Cloudflare Tunnel: https://www.csoonline.com/article/4009636/phishing-campaign-abuses-cloudflare-tunnels-to-sneak-malware-past-firewalls.html
This attack targets end users, not Cloudflare tunnel operators (i.e. self-hosters). It abuses Cloudflare Tunnels as a delivery mechanism for malware payloads, not as a method to compromise or attack people who are self-hosting their own services through Cloudflare Tunnels.
Thanks for clarification!
Good to hear you figured it out with router settings. I’m also new to this but got all that figured out this week. As other commenters say I went with a reverse proxy and configured it. I choose caddy over nginx for easy of install and config. I documented just about every step of the process. I’m a little scared to share my website on public fourms just yet but PM me ill send you a link if you want to see my infrastructure page where I share the steps and config files.
Thanks, I will! Wise of you not to share it publicly for security reasons
If you have a prosumer router I suggest you to use the ddns in the router plus a reverse proxy. This would be the cleanest solution.
If you can not, once everything is working with your external access to the synology, the dsm has a built-in reverse proxy so it can redirect http requests to another server. Although this proxy is really simple and limited it can get the work done if you setup is simple enough.
Thanks! Syno one didn’t work properly, but I got it to work through different means
Check it again, I used it for years before switching to something with more features
Will try!
You’ll need to direct that port for the given service in the router control panel.
For your current server you have a port forwarding for that port already. Just add a port forwarding rule for the new service.
Tried doing that - here’s how I’ve set it up:
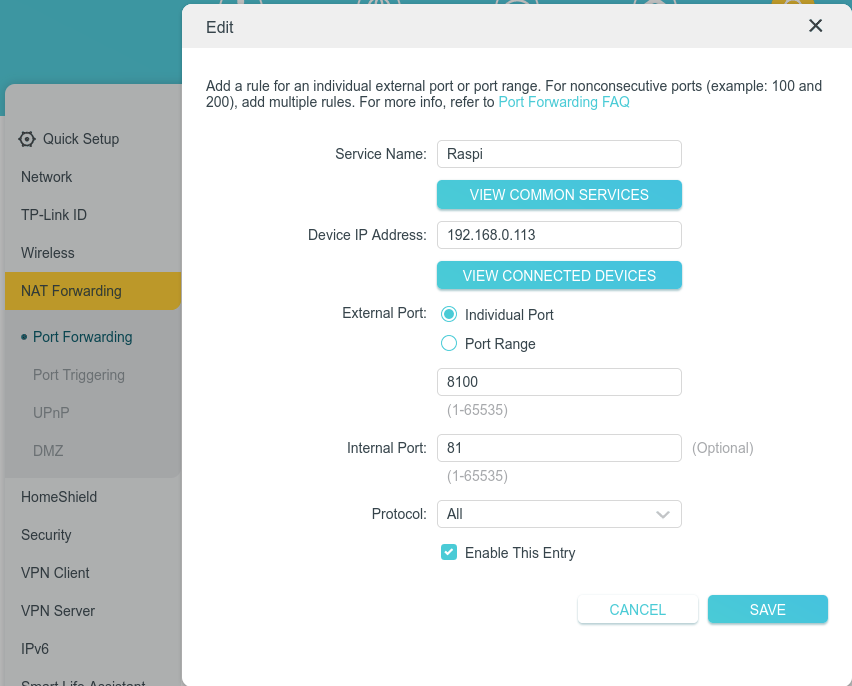
Expected behavior: now when I enter <my domain>:8100, I reach 192.168.0.113:81
Real behavior: connection times out
Stupid question, but is the service reachable at all? What if you map 81 to 81? Or whichever port the other, confirmed-to-work service uses? What if you map that other service to 8100?
Reachable through LAN, but not by URL, even if I port 81 to 81
P.S. Solved! NAS was sitting in the DMZ and this broke forwarding.
What if you try reaching it through your public IP?
Worked eventually, was about DMZ on the router for my NAS
NAT translation, i use my openwrt router for that
OpenWRT also has great IPv6 support