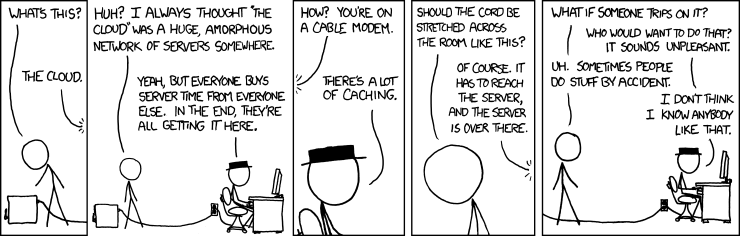
This is why you shouldn’t use cloud services for personal security, because the cloud is just someone else’s computer.
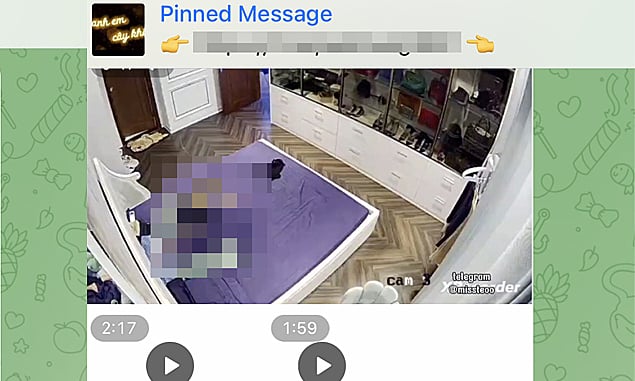
Also, quit putting unnecessary, Internet connected cameras indoors.
I seriously cannot fathom the amount of people that seem to want to put cameras up in their own bedrooms and just let them stream video constantly.
It has nothing to do with any serious home security, and everything to do with mindless consumerism. Hopefully it’s a trend that will pass.
In general, cloud services have far better security than DIY systems. All of the hacked systems in this article are home based systems.
All of the hacked systems in this article are home based systems.
[citation needed] because that’s not in the article. According to the article, attackers used automated scanning software, which strongly implies they brute-forced cameras connected to the Internet with default or weak credentials. That has nothing to do with whether or not the service is based in the cloud.
In general, cloud services have far better security than DIY systems
As a matter of fact, it’s known that the leading cloud-based surveillance system, Ring, has been subject to employee abuse and user accounts have been widely compromised via credential stuffing. In fact, Amazon is currently facing a proposed order from the FTC over the fact that they allowed abuse by employees and more or less knew for years that their lax security practices were placing their customers in danger from cybercriminals. Hell, it’s 2023 and all you have to do to pre-empt most credential stuffing attacks is enforce 2FA, and this was optional in a HOME SECURITY PRODUCT from a LEADING cloud provider. “In general cloud providers have better security” my ass.
Cloud based security only gets better when regulators force cloud providers to improve security, after cloud providers allow hackers to harm thousands to millions of customers.
I’m just gonna say it again: the cloud is just someone else’s computer.
According to the article, attackers used automated scanning software, which strongly implies they brute-forced cameras connected to the Internet with default or weak credentials. That has nothing to do with whether or not the service is based in the cloud.
This is a known problem with popular brands of security cameras sold in Vietnam, that the default configuration has an admin password of “admin” or “12345” accessible from the public Internet. They’re basically sold insecure, and rely on customers to consciously adopt a custom configuration to be secure.
Although, in order to be publicly accessible, one would imagine that they’ve had to configure their firewall to let outside signals to the devices themselves. Or maybe some kind of ddns setup.
Either way, it doesn’t have anything to do with the cloud, and the parent comment is basically right about that.
Although, in order to be publicly accessible, one would imagine that they’ve had to configure …
I’m guessing there are providers in Vietnam offering remote access accounts and apps, the same as 90% of IP security cameras on AliExpress, Amazon, eBay etc. Most of the zero config ones are authenticated with a cloud server 24/7 to enable remote viewing. This being Vietnam specific leads me to believe that the “hackers” are actually a domestic crime org selling compromised hardware; could be as simple as opening the box and obtaining device information (like the serial, MAC, or QR code) before shipping the product.
You can’t connect home system that is never connected to internet, basically make home server and hook up cameras and don’t ever connect that to internet
The problem is cameras like these, the kind that people are putting up inside their own homes, facing their living spaces, their own damn bedrooms, they’re sold to people that have this desire to be able to check in with those cameras remotely at any time, without a good reason.
The only reason my mother seems to have crap like this set up is so she can see the dogs when she’s not home. They’re just sleeping.
Internet connected, living space directed cameras are this bizarre consumer electronics trend that has no legitimate use case for like 90% of the people that rush to use it. Certainly not one that merits the security risks and the privacy invasion that they are inviting on themselves.
Half the reason to own a security camera system is so you can monitor it while away. Can’t do that if the system isn’t online.
Online or cloud-accessed? Those are two separate things.
It’s going to be cloud accessed. People who install these to check on whether Mittens is sleeping aren’t setting up a domain or remembering an IP.
Bro, if I find any ingress point onto your network, I can connect to your networked cams.
Little brother downloads a Trojanised pirate copy of a game? I can connect to your cams via your lil bro’s computer.
Not patched your stuff and there was a drive-by-download and RCE exploit? I can do it through your computer.
Your firewalls are important but they aren’t impenetrable.
Yeah, but you’d pretty much need to target the person so these blanket hacks where a bunch of cameras are exposed aren’t really possible
No I don’t. Like the first example above I can simply trojanise an executable, and release it to the public.
Once I’m on your network, the first thing I’m always going to do is see what I’m working with. That means a network and system info sweep. If I’m efficient, I already have a script to do this.
That sweep will reveal the presence of the camera. I might be interested in extortion material or I can sell this to a criminal gang, if I can get it open. I already have the camera’s MAC address, so finding the make and model isn’t too hard.
Then I might browse to it, see what system software it is running. Then I would try default usernames and passwords (people don’t always change them) and see if there are any usable exploits on the software.
If I come across a certain camera type with certain vulnerabilities a lot, making a script to autofuck these cameras is child’s play.
Source: am an ethical hacker/ red teamer.
Source: am an ethical hacker/ red teamer.
What is the recommended on-ramp for someone with a CS degree and a networking background?
With that kind of background you’ve got a good advantage. You probably know how people fuck up their implementations as rookies, the next step is learning to take advantage of it.
Depending on the areas you want to get into (web, mobile, infrastructure, web3, etc) there are a lot of different training materials you can do. Most are free or very affordable.
Basic infrastructure stuff is a must, but it’s really simple. Your main tool for this will be either Nmap or massscan, both are port-scanners. You need to learn some basic flags and understand why you might want to use some and not others depending on the scenario (you probably already know at least some of this already). This is usually the first technical step in any operation.
Basic Linux and Windows command line is also a must. You don’t need to be able to do Linux From Scratch but you do need to be comfortable with Linux (and Windows) command line; if you manage to get a shell (illicit remote access) on a victim box, this is what you’ll be using to get around. An industry standard toolkit also comes in the form of a Linux distro, namely Kali Linux.
For more advanced infrastructure stuff, check out the HackTricks gitbook, it’s really helpful.
For web (not web3) based stuff, you can start with Damn Vulnerable Web App and OWASP Juice Shop. The former is far more tutorialy but the latter has all sorts of walkthroughs. Understanding why this works is important to understanding in future what kinds of stuff work, which is important when people actually put in (bypassable) protections.
If you want to go through more of a web3 route, get familiar with the Remix IDE and check out Ethernauts.
For mobiles, it’s important to have jailbroken or rooted devices, especially in the case of iOS. Check out Damn Insecure and Vulnerable App (Android) or Damn Vulnerable iOS App (iOS). The OWASP Mobile Testing Guide is also a really useful read.
Once you get comfortable, you can also check out Capture The Flag challenges hosted by other people. CTFTime is a good aggregate for these and HackTheBox is a good training ground for them.
I would generally recommend these tools before going onto certs; once you’re good at these, you’ll breeze through the certs with a light refresher on course details, however the certs are an expensive way to actually learn.
As for which certs, CompTIA Pentest Plus is a good starter. Offensive Security Certified Practitioner (OSCP) is a good mid-level cert, and CTFs are a crazy good preparation (this exam is much more practical-based than your standard exam). Don’t listen to some LinkedIn lunatics that call this a starter exam, it absolutely is not, and they probably have never taken it. It is, however considered something of a gold standard in the industry; if it isn’t a minimum requirement, it is considered VERY helpful in most job applications.
John Hammond’s got some pretty good “getting started with White Hat hacking” videos on his YouTube channel (a lot of “hack a box” and “CTF” style videos). He’s got one or two where he talks about his resume and training/classes he’s done.
Seperate network that’s physically not connected to a network which connects to the internet or cameras with local storage.
You can’t hack into the wildlife camera in my backgarden. It doesn’t even have wifi, just an SD card.
Of course, that’s less useful if you want to check up on your house when you’re away.
That’s what I’ve been trying to say, thank you for backing me up
Vlans
-
not a common feature of home networks
-
If the compromised machine has access to both vlans, you’re still fucked
It’s a feature on mine
That’s why my security has multiple layers
It isn’t a common feature on ISP provided routers, which is what most people use. Some ISPs (example: my own) even make it exceptionally difficult to use other routers. I had to install OpenWRT on my retail router to get it, and getting that working was such a pain.
-
It kinda depends on the setup I think, especially when vlans and firewalls are involved, you’d likely need additional payloads to make further progress in that kind of environment IMO. Something granting persistent remote access to the compromised machine would be the most ideal option.
As always physical access is pretty much game over though lol.
My cams are only accessible via an authenticated endpoint hosted on a dedicated machine, which acts as a “bridge” between the VLAN that the cameras are on (no internet access), and another VLAN hosting internal services, like home assistant, plex etc.
Aside from physical access, the only way to access the cams (that I can think of) would be via some exploit in Home Assistant, or by brute forcing the password to (any of) my network switches to access the management VLAN, changing the VLAN the cameras are set on to something else (bypassing the routing, firewall setup, and auth “bridge” entirely). Or maybe just exploiting the bridge machine directly and dropping a payload to forward the cams out to the net via the services VLAN
With physical access, you could chop up the PoE for an external camera and using that as an ingress point - but you’d only have access to the cameras and the bridge machine unless you exploited that too. At this point the zabbix client on the bridge machine would have notified me that a camera’s dropped off the network, unless you dropped a payload to force it to return a good status lol
Does sound like a very fun exercise though tbh
In general, cloud services have far better security than DIY systems.
Where are you pulling this from? These aren’t “DIY”. DIY is when you roll your own remote network access (e.g. VPN, DDNS, port forwarding, etc) or FOSS software/hardware. I’d trust most DIY systems more than any cloud provider, because most DIY systems would be LAN only or VPN accessible. The QR code authentication mentioned in the article sounds like these are generic IP security cameras of stock firmware, that utilize a cloud server to enable remote viewing over the internet. Even reputable cloud services use the same method to connect or setup individual cams to their cloud.
All of the hacked systems in this article are home based systems.
That doesn’t mean the exploits used are of no fault of the user — from the vendors authentication implementation, software, or hardware.
Maybe, but the difference is a lot more people are going to be looking to target the cloud provider than your home network. To say nothing of the fact that your videos on the cloud are subject to the terms and services that you agree to and those terms can be changed at any time. And also the fact that you can’t guarantee that the stuff you delete off of that server is actually being deleted.
a lot more people are going to be looking to target the cloud provider than your home network.
I can show you logs with tens of thousands of hits from all IPs all over the globe trying to gain access to a single NVR that has a port open on the WAN side of a network.
Besides email servers or FTP servers, cameras are the next highest thing target for attacks. The minute they go online they become a flaming red beacon for hackers.
You have a source for that?
Ok… But cloud services are centralized and have a lot more content to obtain, so that fundamentally makes them a more valuable target. This alone adds a level of relational security to maintaining a home backup of the information. Unless someone happens upon your home network and decides to hack it, or you download a file that sends up a flare, nobody is going to seek it out unless they know you have something specific they want.
Unless someone happens upon your home networ…
If you have an IP camera system exposed to the outside, they will “happen upon you” within the hour.
It’s one of the top things searched for in wide net port scans.
But unlike those cloud services, your home network likely doesn’t have enterprise level threat detection to alert you to it, or a team of network engineers to try to guard against it.
Why the fuck are you broadcasting a beacon to come hack your network? Of course they are going to find it if you light it up like a Christmas tree with a giant neon sign. I said you set up your cameras to record locally. Only an idiot would set up a camera system with an unsecured exposed port. Hell, set up anything with an unsecured exposed port for that matter. Especially one that is an always broadcasting system. It doesn’t even matter if you use a cloud provider at that point. All they have to do is hack an network hop near your home and install a man in the middle and they don’t have to bother hacking a server farm to get your videos.
deleted by creator
LMAO don’t put a fucking camera in your bedroom you dummies
I’d assume fucking cameras are made specifically for the bedroom.
I’m assuming they are in young children’s bedrooms. There’s only one reason to put a camera in an adult’s bedroom ( ͡° ͜ʖ ͡°)
Caring for a bedridden relative?
( ͡° ͜ʖ ͡°)
Counter-Argument: Each camera in a bedroom can be free entertainment for millions!
And don’t stay at hotels or airBnB or …. Well just don’t sleep.
This is what you show people when they say they don’t care about privacy because they have nothing to hide.
We should compile a big list of reasons with sources on top of this one
deleted by creator
Meanwhile, two comments down: “why do people have cameras in their bedroom?”
I know it’s not 100% the same, but there’s a website that gives you access to insecure webcams and has been for ages!
Obviously these aren’t hacked as per the article
Ironic that the website itself is http.
Doesn’t really matter too much, nothing on the website is password protected anyways
just looking around randomly and it’s weird how many of them are private property.
Why is it weird? People get cameras to protect their private property?
sure but not securing them in their own network somehow?
There are driveways, front porches, some sort of office somewhere and even someones 3d printer all with rough coordinates and that’s without actually diving deeper into all of this.
People are lazy and ignorant to the lack of security in the products they buy.
Damn, that website almost has some of everything.
I saw a building that looked like it was waiting to be boarded up. There were some streams with beautiful scenery. There was an official looking meeting room in Greece for, and I even found a stream of a train table!
Yet another reason why IoT crap sucks. You don’t need to put everything on the internet. This one should be obvious.
The “S” in IOT is for “security”.
People don’t think about that. You have to register somewhere in order to use your $12.99 cam, install some app and are good to go.
How would a someone not interested in tech know that the footage data is stored on some online server and you are at the mercy of their itsec.
The question isn’t “how would someone know…?” the question is “do you know what a hacker does?”.
Home assistant tries to keep shit local.
depends on the device.
If the device dont provide local connection, there is nothing home assistant can do about it. Some device will also send data to the cloud even it is locally controlled by HA.
Oh for sure. But unlike smart things or any other hub, only the data that needs a cloud connection will go through the cloud…
Thanks to laziness of the device manufacturers, a lot of them either expose some data endpoints locally, or just use Zigbee which can be easily paired to be used local-only.
Those that require Wi-Fi access can be filtered on the router to disable internet access.
With end to end encryption, and requiring manual key transfer (no key sync), this would not be an issue.
Why the fuck do people put security cameras in their bedrooms? It’s so weird to me that people do this. Even if you think (or at least thought) that you were the only one with access to the footage, won’t the presence of a camera make you feel like you’re being watched? Are we not on camera enough as it is that we have to be on camera in the supposed privacy of our bedrooms? Imagine if you told George Orwell that people would willingly put cameras in their most personal and private spaces.
it’s funny the vnexpress would publish this. vietnamese people are obsessed with security cameras. they see them as a deterrent, or as a way to find the perpetrator later and get all your property back. they put them everywhere.
Hypothetically I want to secure my home with Cameras…
What’s the best way to do this? OSS preferably.
So, just an FYI, I bought Eufy cameras because I believed their marketing bullshit about being secure and end-to-end encrypted. About two months later they changed how they describe their security and quietly modified their privacy policy. Turns out they’re not really end-to-end encrypted and it is possible to gain access to the streams sometimes.
My recommendation, after doing my research is not to buy anything that is able to be viewed remotely. Buy something that stores the video locally, in your home. If possible, buy and install wired cameras.
The most important thing is just to have cameras that are positioned to watch you in bed.
I’m just about to setup TP-link cameras connected to Frigate (NVR software) with a Coral TPU for offline object detection. This means I can block access to internet for the cameras and use a VPN home if I want to watch them.
Zoneminder and any IP camera you can afford.
If you setup wireless you would be best served using a VLAN
Onvif camera (It’s the standard. Any camera that supports onvif will be plug and play). Block the cameras’ Mac addresses at your router so they can’t get out directly. Install zoneminder on Linux. If you need remote access follow all the guides to securing a Linux server that has ports open to the Internet. (Ssl, tailscale etc.)
Blueiris for Windows is great but it’s not open source.
No-internet cameras hooked up to local storage.
For remote access, you could use whatever you want to use for remotely accessing local files.
I use a old phone with IP cam on it, and only allowed local network access connected to my home assistant.
I can view it remotely via home assistant cloud, which is E2EE from instance to phone.
I presume Raspberry Pi Camera is also a great solution. And also I dont put any camera in bedroom or bathroom, because there is no reasonably accessible entrance there.
The first step is to set a strong password.
Not open but https://unify.com/en/
Didn’t they just have a security incident where people could access other people’s full unifi account including devices?
Correct but that’s only if you enable the remote connection through ubiquity, if you have that turned off its all local.
Ah, I wasn’t aware there was an option to keep it local. Does that keep your entire site from being remote manageable or just the camera system?
My understanding is that it’s all or nothing, but I’m not complete sure.
The security issue you mentioned I think only affected when they handle access to the cameras. I think you can set up a VPN and then turn off remote access on the NVR, so it seems possible to avoid that issue.
That being said that’s a lot of work for something they should have handled securely in the first place and doesn’t give me much confidence about their security in general.
It’s an interesting read since the cause of the issue was something to do with a database change that caused an overlap of groups.
Link didn’t work for me there was nowhere to actually buy the videos. Where is the correct link?
deleted by creator
They actually left watermarks with the telegram account on it in the pictures
footages
You’re going to be upset when you fail the 4thbgrade.
No no foot fetish footage, “footages”. They’re calling out foot fetish enjoyers.