I understand that people enter the world of self hosting for various reasons. I am trying to dip my toes in this ocean to try and get away from privacy-offending centralised services such as Google, Cloudflare, AWS, etc.
As I spend more time here, I realise that it is practically impossible; especially for a newcomer, to setup any any usable self hosted web service without relying on these corporate behemoths.
I wanted to have my own little static website and alongside that run Immich, but I find that without Cloudflare, Google, and AWS, I run the risk of getting DDOSed or hacked. Also, since the physical server will be hosted at my home (to avoid AWS), there is a serious risk of infecting all devices at home as well (currently reading about VLANS to avoid this).
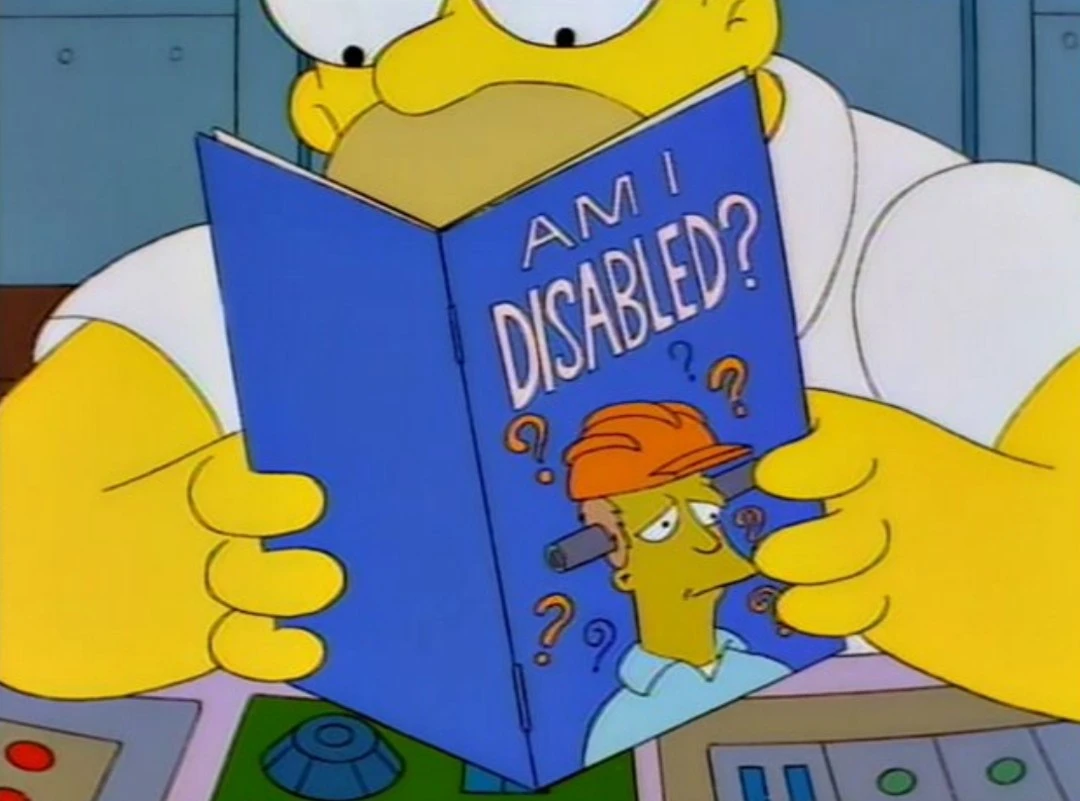
Am I correct in thinking that avoiding these corporations is impossible (and make peace with this situation), or are there ways to circumvent these giants and still have a good experience self hosting and using web services, even as a newcomer (all without draining my pockets too much)?
Edit: I was working on a lot of misconceptions and still have a lot of learn. Thank you all for your answers.
One aspect is how interesting you are as a target. What would a possible attacker gain by getting access to your services or hosts?
The danger to get hacked is there but you are not Microsoft, amazon or PayPal. Expect login attempts and port scans from actors who map out the internets. But I doubt someone would spend much effort to break into your hosts if you do not make it easy (like scripted automatic exploits and known passwords login attempts easy) .
DDOS protection isn’t something a tiny self hosted instance would need (at least in my experience).
Firewall your hosts, maybe use a reverse proxy and only expose the necessary services. Use secure passwords (different for each service), add fail2ban or the like if you’re paranoid. Maybe look into MFA. Use a DMZ (yes, VLANs could be involved here). Keep your software updated so that exploits don’t work. Have backups if something breaks or gets broken.
In my experience the biggest danger to my services is my laziness. It takes steady low level effort to keep the instances updated and running. (Yes there are automated update mechanisms - unattended upgrades i.e. -, but also downwards compatibility breaking changes in the software which will require manual interactions by me.)
+1 for the main risk to my service reliability being me getting distracted by some other shiny thing and getting behind on maintenance.
I’m in this comment.
It’s crowded.
…maybe use a reverse proxy…
+1 post.
I would suggest definitely reverse proxy. Caddy should be trivial in this use case.
cheers,
Reverse proxies don’t add security.
I’m positive that F5’s marketing department knows more than me about security and has not ulterior motive in making you think you’re more secure.
Snark aside, they may do some sort of WAF in addition to being a proxy. Just “adding a proxy” does very little.
So, you’ve gone from:
reverse proxies don’t add security
to:
“adding a proxy” does very little
What’s next?
Give up. You don’t know what the fuck you’re talking about.
… You’re joking right?
No.
May not add security in and of itself, but it certainly adds the ability to have a little extra security. Put your reverse proxy in a DMZ, so that only it is directly facing the intergoogles. Use firewall to only expose certain ports and destinations exposed to your origins. Install a single wildcard cert and easily cover any subdomains you set up. There’s even nginx configuration files out there that will block URL’s based on regex pattern matches for suspicious strings. All of this (probably a lot more I’m missing) adds some level of layered security.
Put your reverse proxy in a DMZ, so that only it is directly facing the intergoogles
So what? I can still access your application through the rproxy. You’re not protecting the application by doing that.
Install a single wildcard cert and easily cover any subdomains you set up
This is a way to do it but not a necessary way to do it. The rproxy has not improved security here. It’s just convenient to have a single SSL endpoint.
There’s even nginx configuration files out there that will block URL’s based on regex pattern matches for suspicious strings. All of this (probably a lot more I’m missing) adds some level of layered security.
If you do that, sure. But that’s not the advice given in this forum is it? It’s “install an rproxy!” as though that alone has done anything useful.
For the most part people in this form seem to think that “direct access to my server” is unsafe but if you simply put a second hop in the chain that now you can sleep easily at night. And bonus points if that rproxy is a VPS or in a separate subnet!
The web browser doesn’t care if the application is behind one, two or three rproxies. If I can still get to your application and guess your password or exploit a known vulnerability in your application then it’s game over.
The web browser doesn’t care if the application is behind one, two or three rproxies. If I can still get to your application and guess your password or exploit a known vulnerability in your application then it’s game over.
Right!?
Your castle can have many walls of protection but if you leave the doors/ports open, people/traffic just passes through.
So I’ve always wondered this. How does a cloudflare tunnel offer protection from the same thing.
They may offer some sort of WAF (web application firewall) that inspects traffic for potentially malicious intent. Things like SQL injection. That’s more than just a proxy though.
Otherwise, they really don’t.
A reverse proxy is used to expose services that don’t run on exposed hosts. It does not add security but it keeps you from adding attack vectors.
They usually provide load balancing too, also not a security feature.
Edit: in other words what he’s saying is true and equal to “raid isn’t baclup”
deleted by creator
All reverse proxies i have used do rudimentary DDoS protection: rate limiting. Enough to keep your local script kiddy at bay - but not advanced stuff.
You can protect your ssh instance with rate limiting too but you’ll likely do this in the firewall and not the proxy.
Use any old computer you have lying around as a server. Use Tailscale to connect to it, and don’t open any ports in your home firewall. Congrats, you’re self-hosting and your risk is minimal.
Exactly what I do and works like a dream. Had a VPS and nginx to proxy domain to it but got rid of it because I really had no use for it, the Tailscale method worked so well.
Drink less paranoia smoothie…
I’ve been self-hosting for almost a decade now; never bothered with any of the giants. Just a domain pointed at me, and an open port or two. Never had an issue.
Don’t expose anything you don’t share with others; monitor the things you do expose with tools like fail2ban. VPN into the LAN for access to everything else.
DDoS and hacking are like taxes: you should be so lucky as to have to worry about them, because that means you’re wildly successful. Worry about getting there first because that’s the hard part.
You don’t have to be successful to get hit by bots scanning for known vulnerabilities in common software (e.g. Wordpress), but OP won’t have to worry about that if they keep everything up to date. However, this is also necessary when renting a VPN from said centralised services.
Well he specified static website, which rules out WP, but yes. If your host accepts posts (in the generic sense, not necessarily specifically the http verb POST) that raises tons of other questions, that frankly were already well addressed when I made my post.
A static website and Immich
he specified static website, which rules out WP
Oops missed that
EDIT: And I missed Immich too
The DDOSED hype on this site is so over played. Oh my god my little self hosted services are going to get attacked. Is it technically possible yes but it hasn’t been my experience.
DDoSing cost the attacker some time and resources so there has to something in it for them.
Random servers on the internet are subject to lots of drive-by vuln scans and brute force login attempts, but not DDoS, which are most costly to execute.
99% of people think they are more important than they are.
If you THINK you might be the victim of an attack like this, you’re not going to be a victim of an attack like this. If you KNOW you’ll be the victim of an attack like this on the other hand…
Many of us also lived through the era where any 13 year old could steal Mommy’s credit card and rent a botnet for that ezpz
My MC server a decade ago was tiny and it still happened every few months when we banned some butthurt kid
DDOS against a little self hosted instance isn’t really a concern I’d have. I’d be more concerned with the scraping of private information, ransomware, password compromises, things of that nature. If you keep your edge devices on the latest security patches and you are cognizant on what you are exposing and how, you’ll be fine.
A VPS with fail2ban is all you need really. Oh and don’t make ssh accounts where the username is the password. That’s what I did once, but the hackers were nice, they closed the hole and then just used it to run a irc client because the network and host was so stable.
Found out by accident, too bad they left their irc username and pw in cleartext. Was a fun week or so messing around with their channels
Talk about a reverse UNO card.
I feel like you have the wrong idea of what hacking acting a actually is… But yes, as long as you don’t do anything too stupid line forwarding all of your ports or going without any sort of firewall, the chances of you getting hacked are very low…
As for DDOSing, you can get DDOSed with or without self hosting all the same, but I wouldn’t worry about it.
Exactly piss off a script kiddie and get ddosed weather your self hosting or not.
Why would anyone ddos you? Ddos costs money andor effort. Noone is going to waste that on you. Maybe dos but not ddos. And the troll will go away after some time as well. There’s no gain in dosing you. Why would anyone hack your static website? For the lulz? If everything is https encrypted on your local net how does a hacker infest everything on your network?
DDOS can happen just from a script hammering on an exposed port trying to brute force credentials.
Then block them there are tools that restrict abuse
You can. I am lucky enough to not have been hacked after about a year of this, and I use a server in the living room. There are plenty of guides online for securing a server. Use common sense, and also look up threat modeling. You can also start hosting things locally and only host to the interwebs once you learn a little more. Basically, the idea that you need cloudflare and aws to not get hacked is because of misleading marketing.
Man if your lucky enough after a year I must be super duper lucky with well over a decade.
Hey no to be harsh or anything but did you actually made your research? Plenty of people self host websites on their house without AWS , Google or Cloudfare and it works fine.
I host a handful of Internet facing sites/applications from my NAS and have had no issues. Just make sure you know how to configure your firewall correctly and you’ll be fine.
You can simply set up a VPN for your home network (e.g. Tailscale, Netbird, Headscale, etc.) and you won’t have to worry about attacks. Public services require a little more work, you will need to rely on a service from a company, either a tunnel (e.g. Tailscale funnel) or a VPS.
mmm netbird seems cool, any experience with it?
No, I’m currently using Tailscale but have been considering switching to Netbird to not be reliant on Tailscale.
Public services require a little more work, you will need to rely on a service from a company, either a tunnel (e.g. Tailscale funnel) or a VPS.
I have been hosting random public services for years publicly and it hasn’t been an issue.
Edit, I might have miss understood the definition of public. I have hosted stuff publicly, however everything was protected by a login screen. So it wasn’t something a random person could make use of.
Other than the low chance of you being targeted I would say only expose your services through something like Wireguard. Other than the port being open attackers won’t know what it’s for. Wireguard doesn’t respond if you don’t immediately authenticate.
If you are afraid of being ddosed which is very unlikely. Cloudflare has free ddos protection. You can put some but not all things behind their proxy.
Also instead of making things publicly available look in to using a VPN. Wireguard with “wireguard easy” makes this very simple.
VLANs do not make you network magically more secure. But when setup correctly can increase security a load if something has already penetrated the network. But also just to streamline a network and allow or deny some parts of the network.