Our local sheriff is using some spy level shit in our county that he refuses to explain.
He keeps “happening” upon crimes just “on accident.” yesterday it was “stopped to take a pee in public park and caught a baddie” and two days before that it was “just happen to follow and pull over a guy with lots of pounds of pot hidden in the car.”
The US police are spying on Americans phones, internet, GPS, and everything with no judicial recourse because it is corporations spying and then “giving the info” to the police for money.
The US law enforcement has gone full STAZI but using capitalism as additional cover.
The US is dead.
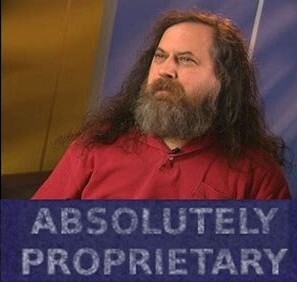
Let’s all apologize to Stallman.
the man has rarely been proven wrong in anything tech related he has said
Let’s all apologize to Stallman.
For the twice a day that broken toe-jam-eating watch is right?
They’re probably just capturing SMS messages or regular calls. Which is still illegal without a warrant, but who watches the watchers? Use encrypted chats and encrypted calls if you’re worried.
“on accident“ 🤮
“on accident“ 🤮
I know. Who SAYS that? It’s by accident. One doesn’t plan these things.
'Round here we say “with accident” or “of accident”, thank you
As the old and venerable neuromonkey once said:
Welp. Just let the nukes fly, then. First it’s “on accident,” and before long you’ve got meth addicted baby prostitute warlords running the local Walmart.
That’s also a red flag for a dirty cop getting information from criminal group A to go after competition.
You should probably move.
Mind telling us which sherrif this is?
I think it’s the one in New York named Spyder Mann
Without knowing how they got into his phone, this is a non-story that is just a retelling of older stories. For all we know they just took his dead finger and put it on the reader. Or maybe he used the same 4-digit PIN for his debit card or lock box or something else that they were able to recover. Maybe some detective just just randomly entered the shooter’s birthday, only to say “Hey sarge, you’re never gonna believe this… first try!”
There’s nothing useful that can be taken away from this story yet, until more details come out.
they just took his dead finger and put it on the reader.
My bet’s on this.
Exactly. The article doesn’t shy away from a bit of free publicity for Cellerite. Which is nowhere near as much of a magic bullet as the “tech media” makes it out to be.
How do I know it? By doing the most basic of research by heading to their website and looking at their manuals and documentation.
And Cellerite won’t tell you this publicly because their bottom line depends on their ability to massively overprice their services which they sell to technically illiterate people.
Any article that mentions Cellerite without a caveat about the dubiousness of their publicity can be disregarded and shouldn’t be taken seriously.
I’m super curious how they got into his phone
“We tried 0000. Tony, write up a press release about how incredible we are at our job and how we spent 400% of our usual overtime on it and send it to the tech press. Make sure they mention we need to triple next year’s budget for security and shit.”
Good chance it was just putting the dead dudes finger on the scanner lmao
I’m pretty sure it used to be easier with phones that didn’t have full disk encryption.
The article does mention Cellebrite.
stingrays, people.
they sell the exploits and are all hush hush about it.
Stingrays don’t do shit for this. That’s mostly real time location data focused in by tricking your phone into reporting its location to a fake cell tower controlled by an adversary. That doesn’t get into the data in your phone, and even if someone used the fake tower to man in the middle, by default pretty much all of a phone’s Internet traffic is encrypted from the ISP.
The world of breaking disk encryption on devices is a completely different line of technology, tools, and techniques.
stingrays can compromise a phone through modem exploits, and pull data from there.
though not all of them are made equal, they are an entire category of devices.
Oh damn, just read about these baseband exploits. Ok, you’ve changed my mind.
Easier is a very relative term. It’ll be really expensive to use a genuine zero-day to do it. Such exploits are few and far between.
But known exploits that have been patched, but not applied because they didn’t update their phone, are plentiful enough.
Update your phones. Reboot them regularly, too.
This is true, but becoming an increasingly less important factor because devices now ship with automatic updates enabled by default.
Personally, if I had to guess as someone who studies exploits for a living, I’d wager the device isn’t the most recent model and is probably a few years old, so there are likely known unpatchable bootrom or firmware bugs that can be used from their private arsenal without having to risk an actual zero day exploit.
This is the would be assassin’s phone.
They gave that to the NSA or FBI Counter Intel guys who are hooked in with NSA.
Your phone is not going there.
However I would be on the lookout for that tech coming down the pipelines.
https://www.404media.co/leaked-docs-show-what-phones-cellebrite-can-and-cant-unlock/
Google Pixels are on the list but Graphene isn’t.
Ayyyy graphene gang
Do they say what phone it was?
Yeah my guess is some shitty android.
Guys I think they meant from a bad OEM.
I did and I said that. A shitty android. If I meant to say that all android are shitty I would have just said “must’ve been an android”
Edit" apparenyly “mist-ve” is more of a word than “must’ve” according to my keyboard.
This is the best summary I could come up with:
Just two days after the attempted assassination at former President Donald Trump’s rally in Butler, Pennsylvania, the FBI announced it “gained access” to the shooter’s phone.
Cooper Quintin, a security researcher and senior staff technologist with the Electronic Frontier Foundation, said that law enforcement agencies have several tools at their disposal to extract data from phones.
The bureau famously butted heads with Apple in late 2015 after the company refused to help law enforcement get around the encryption on the San Bernardino, California shooter’s iPhone.
Early in the following year, Apple refused a federal court order to help the FBI access the shooter’s phone, which the company said would effectively require it to build a backdoor for the iPhone’s encryption software.
“The FBI may use different words to describe this tool, but make no mistake: Building a version of iOS that bypasses security in this way would undeniably create a backdoor,” Cook wrote.
Riana Pfefferkorn, a research scholar at the Stanford Internet Observatory, said the Pensacola shooting was one of the last times federal law enforcement agencies loudly denounced encryption.
The original article contains 1,208 words, the summary contains 180 words. Saved 85%. I’m a bot and I’m open source!
Can they access Pixel 8 with GrapheneOS? I think not
Depends, is your bootloader unlocked ?
Locked and USB-C Off on firmware level
Never keep anything on your phone that would require you to lock it.
I’ve never locked my phone.
It’s true, I have their mom’s phone number.
Son of a bitch! Stop calling so late!
Paid by everybodies taxes™️
For GrapheneOS full disk encryption, am I correct in understanding that the disk is encrypted when my phone is locked and decrypted when I unlock it? So I don’t need to turn it off for it to be encrypted, as long as it’s locked it’s encrypted?
The disk is encrypted when the phone is off, and it is decrypted after you turn it on and authenticate locally.
Thanks, that makes sense.
A 2020 investigation by the Washington, DC-based nonprofit organization Upturn found that more than 2,000 law enforcement agencies in all 50 states and the District of Columbia had access to mobile device forensic tools (MDTFs).